At my company AppCove, we have our own certificate authority that we use with development servers and sites. This allows us to (at no additional cost) use HTTPS and SSL for all of these alternate domains and subdomains.
The downside is that our certificate is not trusted by any stock browser or operating system.
Therefore, to prevent getting an ugly and scary SSL warning, anyone who needs to visit these (private audience) sites must first “trust” our certificate authority.
A note on security. If you are telling your computer to trust a certificate authority, then you must really actually “trust” that authority. If the signing key fell into the wrong hands, then they could create fake certificates for other sites you visit, like http://www.google.com, and intercept your data. At AppCove, we use aggressive security measures to protect the certificate authority key (as we do for customer data and applications).
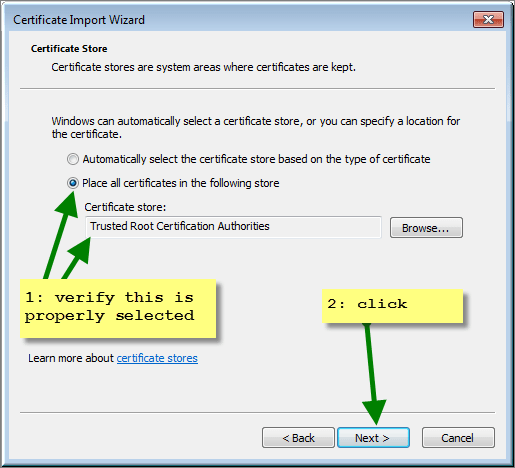
In this example, I am causing my Windows 7 workstation to trust appcove-ca-cert.pem.crt
— Start of slight detour —
If you want to verify it was installed, do this. Otherwise, skip the next 2 screens.
— End of slight detour —
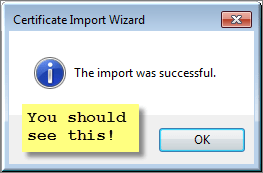
At this point, you should be able to visit any HTTPS site that was signed with this certificate authority and your browser will indicate that it is a secure connection.